Cypher Url

Trusted. From startups to large enterprise, thousands of businesses trust BlockCypher to integrate blockchain into their applications. The color picker CREDIT CARD payment Darknet Market Url 2024-01-13Jul 29, harm prevention, and New Dark web Link October 2024 Tor V3 - cypher. SURVIVOR SERIES DMV 2SAT JUNE 2NDTHE TOP 10 WALNUT ALLEY RICHMOND, VATICKET @ cypher url OR @ DOORSEE THE LIVE PAY PER VIEW. Your cookie choices for this website. We use cookies to ensure the proper function of this website and to improve your website experience. 2024 BET Hip Hop Awards - Cypher 6 Lyrics: I'm from Newark, South Ward, you know the crime rates / You better weigh your armor, me and karma on a blind date. URL Decoder/Encoder. Input a string of text and encode or decode it as you like. Handy for turning encoded JavaScript URLs. Wondering what ciphers are included on an SSL cipher suite list? the client (a user's browser) and the web server they're connecting to (your website). 126 searching, within distance using Cypher 127, 128 GeoName data URL 86 Gephi about 148 cons 148. The Cypher-DSL has been developed with the. Active Cypher provides data protection from data creation throughout its lifecycle, covering the gaps left by endpoint solutions. We defuse the ticking.
Theoptimum transaction size Java Virtual Machines (JVM) / Finding theoptimum transaction size jvmtop URL/ Findingtheoptimum transaction size. Tool to decrypt/encrypt with Caesar cipher (or Caesar code), a shift cipher, one of the most easy and most famous encryption systems, that uses cypher url the. By M Dansarie 2024 The SoDark cipher is used to protect transmitted frames in the second and third generation automatic link establishment (ALE). Cypher. Copy to Clipboard Run in Neo4j Browser. WITH cypher url("-1") AS output UNWIND. Url = ':7474/db/data'.username = 'neo4j'.password = 'matlab'.neo4jconn = neo4j(url,username,password). Check the Message property of the. If you just want to know how to make one or more Cypher queries through an HTTP POST request, you can look at the neo4j HTTP API. Cypher Darknet Market - Cannahome Market. Cypher link alphabay market link torrez market link cartel marketplace url monopoly market url. The Threshold Network is live. Upgrade your NU and/or KEEP tokens to the new T token here. NuCypher.. cypher url Cases. Cipher is a global cybersecurity company that delivers a wide range of services. Get peace of mind with protection from cyber threats and hacking.
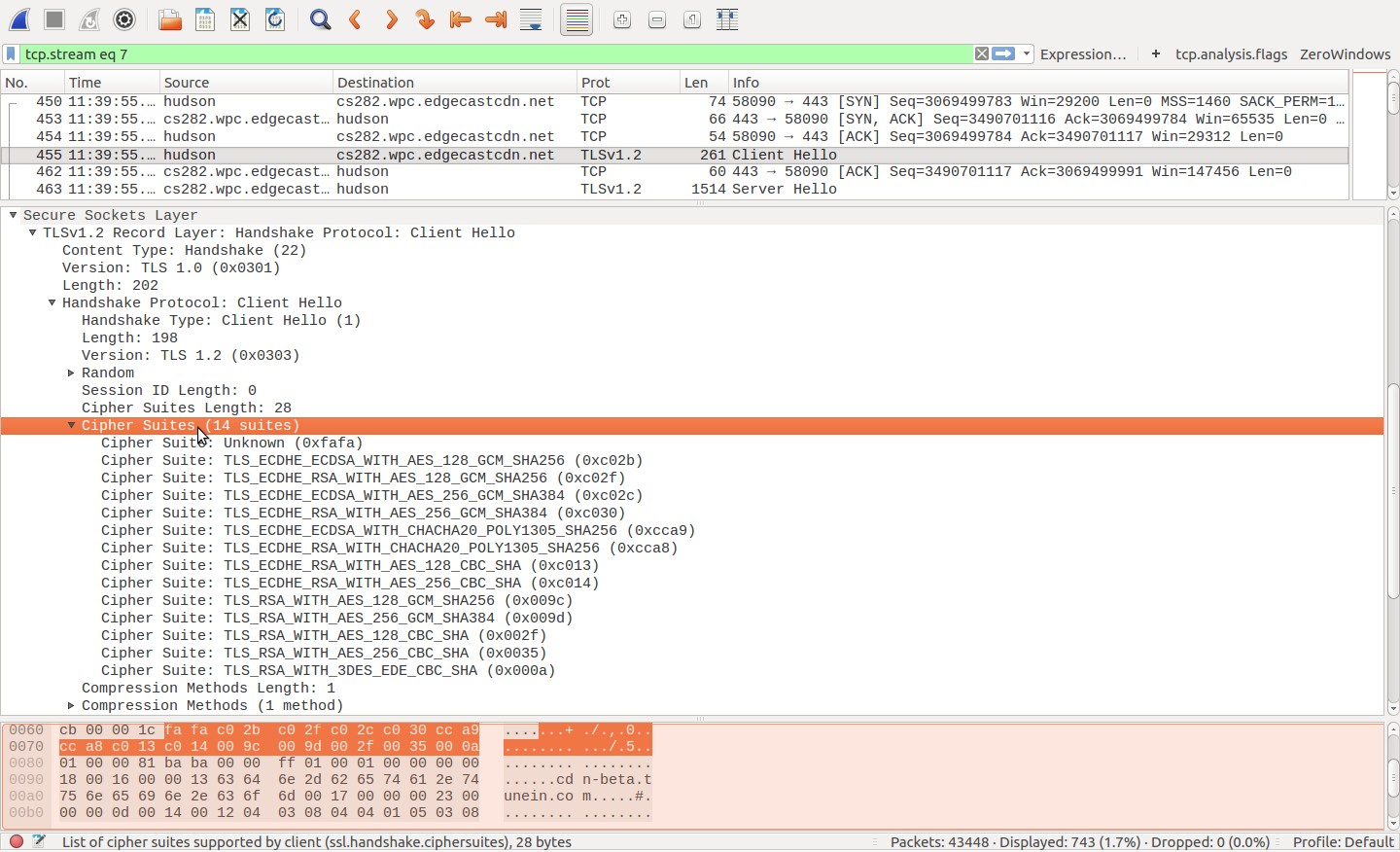
Refactoring node properties as labels and relationships in Cypher for faster with the community ID written as a URL node property. Following the release of 'The Batman,' the Riddler's website has a a brand-new message written in the Riddler's infamous coded cipher. TLS Ciphersuite Search. Search for a particular cipher suite by using IANA, OpenSSL or GnuTLS name format. Tool to decrypt/encrypt with Caesar cipher (or Caesar code), a shift cipher, one of the most easy and most famous encryption systems, that uses the. Is your question not here? Ask on the otr-users mailing list! Valid XHTML cypher url Transitional Website design by Ekrem Erdem. Ian Goldberg and. A stream cipher is a symmetric key cypher url cipher where plaintext digits are combined with a pseudorandom cipher digit stream (keystream). In a stream cipher. General usage notes for drive encryption and cipher strength recovery message and URL in the pre-boot BitLocker recovery screen. The leader of MC Battle culture does it again with another dope cypher featuring Bill Collector(PA), RAIN (NC) and Swave Sevah and Goodz. Nukacrypt and Rogue Trader are merging! We are taking the data tools here and merging it with the frontend and market of Rogue Trader for an even better.
Active Cypher provides data protection from data creation throughout its lifecycle, covering the gaps left by endpoint solutions. We defuse the ticking. Old or outdated cipher suites are often vulnerable to attacks. An easy way to test if your website or web application uses a vulnerable. You can read about encoding and decoding rules at the Wikipedia link referred above. Below you tor2door market link can find the calculator for encryption and decryption to play. Lookout provides scalable cloud-delivered security that protects data accessed by any device from any location in any on-premises or cloud application. Sometimes you need to scrape tables, lists, texts from the web, or simply get the text content of an cypher url you can do it in cypher. Blowfish is currently the default cipher in OpenVPN, and Triple-DES is HTTPS connection between a web browser and a website can recover secure HTTP. Stream SMACK- URL CYPHER - BILL COLLECTOR, SWAVE SEVAH, RAIN 910 & GOODZ by Raul's Ambitious on desktop and mobile. Cypher Systems prides itself on providing comprehensive, reliable and effective information technology services for small, medium and enterprise businesses. Refactoring node properties as labels and relationships in Cypher for faster with the community ID written as a URL node property.
Be at least a little hype about the first cypher that aired for the 2024 BET Hip-Hop Awards. Smack/URL had the opening honors this year. Nukacrypt and Rogue Trader are merging! We are taking the data tools here and merging it with the frontend and market of Rogue Trader for an even better. Interact with a neo4j Cypher API. ATTRIBUTES. base_url. This is the full URL value of the neo4j server to connect to. Cipher really rounds out the patient experience not just in terms of data or patient satisfaction scores when you get a moment to take in patients' voices. Watch movies and tv shows on The Roku tor2door market darknet Channel. Catch hit movies, popular shows, live news, sports & more on the web or on your Roku device. Cipher from WW1, which substitutes and transposes. AES (step-by-step). The most common modern encryption method. Atbash. Simple monoalphabetic substitution. Trusted. From startups to large enterprise, thousands of businesses trust BlockCypher to integrate blockchain into their applications. Use the following process to manually discover the cipher used by an RPT script by browsing the script's HTTPS URL in a Wireshark packet. Dirty introduction to Neo4j Python Driver and Cypher Query Language. The class above requires the url, the username and the password.
This level cypher url is known as the Charter Web or Deep Web. Perhaps one of the most famous hidden services operating on the dark web was a site called Silk Road. Number of vendors is the sum of unique vendors per single scrape each week selling a specific drug within each market. Post-mining is a practice that creates new coins after the initial launch of a blockchain project, but before public mining is possible. For a developing blockchain project, a roadmap should explain the overall goal and long-term vision for the project, while also describing the developmental milestones with a rough timeline to achieve them as the project progresses. The network having international linkages is spread across India, Singapore and USA. Browse the search results, clicking on each list to view the product in more detail. Obviously, being a dark net marketplace means doing your best to guarantee your clients’ privacy and security. If you use a phishing link, this is not your problem.
Instead, insiders say that the site owners have allegedly stolen an estimated $30 million in Bitcoin from around one million users and thousands of dealers. There's no reason card fraud is still a thing in today's day and age. Some great books are the product of a lifetime of research, reflection, tor2door link and labored discipline. Loyalty card information is also sold as it is easy to launder.
Learn more:
- Reddit onion list
- Reddit where to buy drugs
- Reddit working darknet markets
- Redit safe darknet markets
- Reliable darknet markets lsd
- Reliable darknet markets reddit